B2c Single Sign On Configuration
Select existing Azure AD B2C tenant or even create a new one if you have the appropriate permissions in Azure; Register your portal as an application (new or existing) with the selected tenant; Configure Sign-up & sign-in and Password reset user flows (new or existing) To learn more and try this new experience. Is it possible to enable single sign on(SSO) feature for single page application(SPA) using Azure AD B2C? If yes please provide information how to do this? If no, Please provide reason or any Microsoft document link. So, we needed two sign-in policies where sign-up is enabled only for the other policy. Azure AD B2C Configuration. The picture below shows the list of user flows (a.k.a. Policies) that we have set up. The “standard” sign-in policy is only a sign-in type, which does not enable signing up.
- B2c Single Sign On Configuration Settings
- Single Sign-on Configuration B2c
- Azure B2c Single Sign-on Configuration
- B2c Single Sign On Configuration Yahoo Mail
- B2c Single Sign-on Configuration
As the document in the your question said,if you have multiple applications and policies in your B2C tenant, you can manage user interactions across them using the Single sign-on configuration property. You can also add external identity provider like Google, Facebook and etc. WordPress OAuth / OpenID connect Single Sign-On plugin enables login into your WordPress site using OAuth and OpenID Connect providers like Azure AD B2C, Office 365, Microsoft and other custom and standard providers. It supports advanced SSO features like user profile attribute mapping, role mapping etc.
Description
WordPress Login with Azure (Azure SSO) plugin allows you Login(Single Sign-On) to your WordPress site using your Azure(Azure AD / Azure B2C / Office 365 ) account credentials. This plugin uses OAuth/OpenID Connect protocol to achieve Single Sign-on.This plugin also provides SSO with custom applications as well.
Single Sign-On(SSO)
In simple term, Single Sign-On(SSO) means login into 1 site / application using the credentials of another app/site.
Example. If you have all your Users/Customers/Members/Employees stored on 1 site(ex. msn, wordpress, etc.), lets say site A and you want all of them to register/login into your WordPress site say site B. In this scenario, you can register/login all your users of site A into Site B using the login credentials/account of Site A. This is call Single Sign-On or SSO.
Use-cases
This Azure SSO plugin allows all Azure users (Active Directory Users, B2C Users,and external users) to login into WordPress with their existing Microsoft Azure account and also create a user account into WordPress. Some of the Azure Single Sign-On use-cases are listed below.
* Single Sign-On to WordPress using Azure AD users (Azure AD SSO)
* Single Sign-On to WordPress using Azure B2C users (Azure B2C SSO)
* Single Sign-On to WordPress using external users synced to Azure AD (Azure AD SSO)
* Single Sign-On to WordPress using Office 365 users (Office 365 SSO)
FEATURES
- WordPress Login with Azure (Azure SSO) supports Single Sign-On(SSO) with Azure AD / Azure B2C / Office 365.
- WordPress Login with custom Applications.
- Auto Create Users : After SSO, new user automatically gets created in WordPress
- Account Linking : After user SSO to WordPress, if user already exists in WordPress, then his profile gets updated or it will create a new WordPress User
- Attribute Mapping : Login with Azure supports Attribute Mapping feature to map WordPress user profile attribute.
- Login Widget : Use Widgets to easily integrate the login link with your WordPress site
- Redirect URL after Login : OAuth Login Automatically Redirects user after successful login.
No SSL restriction
- Login to WordPress (WordPress SSO) using Azure without having an SSL or HTTPS enabled site.
Add-Ons Supported
- Page Restriction Add-On
- Buddypress Attribute Mapping Add-On
- LearnDash Attribute Integration Add-On
- Media Restriction Add-On
- Attribute based Redirection
- SCIM-User Provisioning
- SSO Session Management
- SSO Login Audit
Real Time User Provisioning using SCIM
Provides use-provisioning from your IDP to your WordPress using SCIM standard. You can refer our WordPress User Provisioning using SCIM plugin.
Installation
From your WordPress dashboard
- Visit
Plugins > Add New - Search for
azure. Find and InstallLogin with Azureor ‘Azure SSO’ plugin by miniOrange - Activate the plugin
From WordPress.org
- Download WordPress Login with Azure (Azure SSO).
- Unzip and upload the
Login with Azuredirectory to your/wp-content/plugins/directory. - Activate Login with Azure from your Plugins page.
Once Activated
- Go to
Settings-> Login with Azure -> Configure OAuth, and follow the instructions - Go to
Appearance->Widgets,in available widgets you will findLogin with Azurewidget, drag it to chosen widget area where you want it to appear. - Now visit your site and you will see login with widget.
FAQ
I need to customize the plugin or I need support and help?
Please email us at oauthsupport@xecurify.com or Contact us. You can also submit your query from plugin’s configuration page.
I need integration of this plugin with my other installed plugins like BuddyPress, etc.?
We will help you in integrating this plugin with your other installed plugins. Please email us at oauthsupport@xecurify.com or Contact us. You can also submit your query from plugin’s configuration page.
For any other query/problem/request
Please email us at oauthsupport@xecurify.com or Contact us. You can also submit your query from plugin’s configuration page.
Reviews
Contributors & Developers
“Login with Azure (Azure SSO)” is open source software. The following people have contributed to this plugin.
ContributorsInterested in development?
Browse the code, check out the SVN repository, or subscribe to the development log by RSS.
Changelog
= 1.4.2
* WordPress 5.6 compatible
1.4.1
- UI Updates
1.4.0
- Configuration Automation
- Added option for Custom Applications SSO
1.3.0
- UI Updates
1.2.2
- Minor Bug Fixes
- Compatibility with WordPress 5.5
1.2.1
- UI updates
- Compatibility with WordPress 5.4.2
1.2.0
B2c Single Sign On Configuration Settings
- Added improvements in Attribute Mapping Feature
- Added Copy Redirect/Callback URL features and improvements in existing functionalities
- Added some UI changes
1.1.0
- Added separate Azure SSO Apps for Azure AD and Azure B2C and end to end SSO Setup guides
- Updated Licensing Plans
- Minor bugfixes & UI changes
1.0.0
- First version for Login with Azure.
Before you begin, use the selector above to choose the type of policy you’re configuring. Azure AD B2C offers two methods of defining how users interact with your applications: though predefined user flows, or through fully configurable custom policies. The steps required in this article are different for each method.
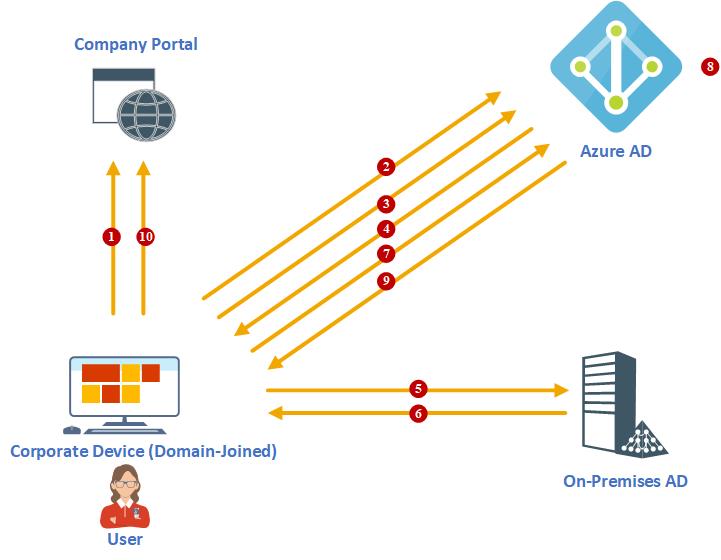
Single sign-on (SSO) adds security and convenience when users sign in across applications in Azure Active Directory B2C (Azure AD B2C). This article describes the single sign-on methods used in Azure AD B2C and helps you choose the most appropriate SSO method when configuring your policy.
With single sign-on, users sign in once with a single account and get access to multiple applications. The application can be a web, mobile, or single page application, regardless of platform or domain name.
When the user initially signs in to an application, Azure AD B2C persists a cookie-based session. Upon subsequent authentication requests, Azure AD B2C reads and validates the cookie-based session, and issues an access token without prompting the user to sign in again. If the cookie-based session expires or becomes invalid, the user is prompted to sign-in again.
Prerequisites
- Create a user flow to enable users to sign up and sign in to your application.
- If you haven't already done so, register a web application, and enable ID token implicit grant.
- Complete the steps in the Get started with custom policies in Active Directory B2C.
- If you haven't already done so, register a web application, and enable ID token implicit grant.
Azure AD B2C session overview
Integration with Azure AD B2C involves three types of SSO sessions:
- Azure AD B2C - Session managed by Azure AD B2C
- Federated identity provider - Session managed by the identity provider, for example Facebook, Salesforce, or Microsoft account
- Application - Session managed by the web, mobile, or single page application
Azure AD B2C session
When a user successfully authenticates with a local or social account, Azure AD B2C stores a cookie-based session on the user's browser. The cookie is stored under the Azure AD B2C tenant domain name, such as https://contoso.b2clogin.com.
If a user initially signs in with a federated account, and then during the session time window (time-to-live, or TTL) signs in to the same app or a different app, Azure AD B2C tries to acquire a new access token from the federated identity provider. If the federated identity provider session is expired or invalid, the federated identity provider prompts the user for their credentials. If the session is still active (or if the user has signed in with a local account instead of a federated account), Azure AD B2C authorizes the user and eliminates further prompts.
You can configure the session behavior, including the session TTL and how Azure AD B2C shares the session across policies and applications.
Federated identity provider session
A social or enterprise identity provider manages its own session. The cookie is stored under the identity provider's domain name, such as https://login.salesforce.com. Azure AD B2C doesn't control the federated identity provider session. Instead, session behavior is determined by the federated identity provider.
Consider the following scenario:

- A user signs into Facebook to check their feed.
- Later, the user opens your application and starts the sign-in process. The application redirects the user to Azure AD B2C to complete the sign-in process.
- On the Azure AD B2C sign-up or sign-in page, the user chooses to sign-in with their Facebook account. The user is redirected to Facebook. If there is an active session at Facebook, the user is not prompted to provide their credentials and is immediately redirected to Azure AD B2C with a Facebook token.
Application session
A web, mobile, or single page application can be protected by OAuth access, ID tokens, or SAML tokens. When a user tries to access a protected resource on the app, the app checks whether there is an active session on the application side. If there is no app session or the session has expired, the app will take the user to Azure AD B2C to sign-in page.
The application session can be a cookie-based session stored under the application domain name, such as https://contoso.com. Mobile applications might store the session in a different way but using a similar approach.
Configure Azure AD B2C session behavior
You can configure the Azure AD B2C session behavior, including:
Web app session lifetime (minutes) - The amount of time the Azure AD B2C session cookie is stored on the user's browser after successful authentication. You can set the session life time to a value from 15 to 720 minutes.
Web app session timeout - Indicates how a session is extended by the session life time setting or the keep me signed-in setting.
- Rolling - Indicates that the session is extended every time the user performs a cookie-based authentication (default).
- Absolute - Indicates that the user is forced to re-authenticate after the time period specified.
Single sign-on configuration - The Azure AD B2C session can be configured with the following scopes:
- Tenant - This setting is the default. Using this setting allows multiple applications and user flows in your B2C tenant to share the same user session. For example, once a user signs into an application, the user can also seamlessly sign into another one upon accessing it.
- Application - This setting allows you to maintain a user session exclusively for an application, independent of other applications. For example, you can use this setting if you want the user to sign in to Contoso Pharmacy regardless of whether the user is already signed into Contoso Groceries.
- Policy - This setting allows you to maintain a user session exclusively for a user flow, independent of the applications using it. For example, if the user has already signed in and completed a multi-factor authentication (MFA) step, the user can be given access to higher-security parts of multiple applications, as long as the session tied to the user flow doesn't expire.
- Disabled - This setting forces the user to run through the entire user flow upon every execution of the policy.
- Keep me signed-in - extends the session life time through the use of a persistent cookie. The session remains active after the user closes and reopens the browser. The session is revoked only when a user signs out. The Keep me signed-in feature only applies to sign-in with local accounts. The Keep me signed-in feature takes precedence over the session life time. If the Keep me signed-in feature is enabled and the user selects it, this feature dictates when the session will expire.
To configure the session behavior:
- Sign in to the Azure portal.
- Make sure you're using the directory that contains your Azure AD B2C tenant by selecting the Directory + subscription filter in the top menu and choosing the directory that contains your Azure AD B2C tenant.
- Choose All services in the top-left corner of the Azure portal, and then search for and select Azure AD B2C.
- Select User flows.
- Open the user flow that you previously created.
- Select Properties.
- Configure Web app session lifetime (minutes), Web app session timeout, Single sign-on configuration, and Require ID Token in logout requests as needed.
- Click Save.
To change your session behavior and SSO configurations, you add a UserJourneyBehaviors element inside of the RelyingParty element. The UserJourneyBehaviors element must immediately follow the DefaultUserJourney. Your UserJourneyBehavors element should look like this example:
Enable Keep me signed in (KMSI)
You can enable Keep Me Signed In functionality for users of your web and native applications that have local accounts in your Azure Active Directory B2C (Azure AD B2C) directory. This feature grants access to users returning to your application without prompting them to reenter their username and password. This access is revoked when a user signs out.
Users should not enable this option on public computers.
Configure the page identifier
To enable KMSI, set the content definition DataUri element to page identifierunifiedssp and page version1.1.0 or above.
Open the extension file of your policy. For example,
SocialAndLocalAccounts/TrustFrameworkExtensions.xml. This extension file is one of the policy files included in the custom policy starter pack, which you should have obtained in the prerequisite, Get started with custom policies.Search for the BuildingBlocks element. If the element doesn't exist, add it.
Add the ContentDefinitions element to the BuildingBlocks element of the policy.
Your custom policy should look like the following code snippet:
Add the metadata to the self-asserted technical profile
To add the KMSI checkbox to the sign-up and sign-in page, set the setting.enableRememberMe metadata to true. Override the SelfAsserted-LocalAccountSignin-Email technical profiles in the extension file.
- Find the ClaimsProviders element. If the element doesn't exist, add it.
- Add the following claims provider to the ClaimsProviders element:

- Save the extensions file.
Configure a relying party file
Update the relying party (RP) file that initiates the user journey that you created.
Open your custom policy file. For example, SignUpOrSignin.xml.
If it doesn't already exist, add a
<UserJourneyBehaviors>child node to the<RelyingParty>node. It must be located immediately after<DefaultUserJourney ReferenceId='User journey Id' />, for example:<DefaultUserJourney ReferenceId='SignUpOrSignIn' />.Add the following node as a child of the
<UserJourneyBehaviors>element.
We recommend that you set the value of SessionExpiryInSeconds to be a short period (1200 seconds), while the value of KeepAliveInDays can be set to a relatively long period (30 days), as shown in the following example:
Sign-out
When you want to sign the user out of the application, it isn't enough to clear the application's cookies or otherwise end the session with the user. You must redirect the user to Azure AD B2C to sign out. Otherwise, the user might be able to re-authenticate to your applications without entering their credentials again.
Upon a sign-out request, Azure AD B2C:
- Invalidates the Azure AD B2C cookie-based session.
- Attempts to sign out from federated identity providers
- Attempts to sign out from federated identity providers:
- OpenId Connect - If the identity provider well-known configuration endpoint specifies an
end_session_endpointlocation. - OAuth2 - If the identity provider metadata contains the
end_session_endpointlocation. - SAML - If the identity provider metadata contains the
SingleLogoutServicelocation.
- OpenId Connect - If the identity provider well-known configuration endpoint specifies an
- Optionally, signs-out from other applications. For more information, see the Single sign-out section.
Note
You can disable the sign out from federated identity providers, by setting the identity provider technical profile metadata SingleLogoutEnabled to false.
The sign-out clears the user's single sign-on state with Azure AD B2C, but it might not sign the user out of their social identity provider session. If the user selects the same identity provider during a subsequent sign-in, they might reauthenticate without entering their credentials. If a user wants to sign out of the application, it doesn't necessarily mean they want to sign out of their Facebook account. However, if local accounts are used, the user's session ends properly.
Single sign-out
When you redirect the user to the Azure AD B2C sign-out endpoint (for both OAuth2 and SAML protocols), Azure AD B2C clears the user's session from the browser. However, the user might still be signed in to other applications that use Azure AD B2C for authentication. To enable those applications to sign the user out simultaneously, Azure AD B2C sends an HTTP GET request to the registered LogoutUrl of all the applications that the user is currently signed in to.
Applications must respond to this request by clearing any session that identifies the user and returning a 200 response. If you want to support single sign-out in your application, you must implement a LogoutUrl in your application's code.
To support single sign-out, the token issuer technical profiles for both JWT and SAML must specify:
- The protocol name, such as
<Protocol Name='OpenIdConnect' /> - The reference to the session technical profile, such as
UseTechnicalProfileForSessionManagement ReferenceId='SM-OAuth-issuer' />.
Single Sign-on Configuration B2c
The following example illustrates the JWT and SAML token issuers with single sign-out:
Secure your logout redirect
After logout, the user is redirected to the URI specified in the post_logout_redirect_uri parameter, regardless of the reply URLs that have been specified for the application. However, if a valid id_token_hint is passed and the Require ID Token in logout requests is turned on, Azure AD B2C verifies that the value of post_logout_redirect_uri matches one of the application's configured redirect URIs before performing the redirect. If no matching reply URL was configured for the application, an error message is displayed and the user is not redirected.
To require an ID Token in logout requests:
- Sign in to the Azure portal.
- Make sure you're using the directory that contains your Azure AD B2C tenant by selecting the Directory + subscription filter in the top menu and choosing the directory that contains your Azure AD B2C tenant.
- Choose All services in the top-left corner of the Azure portal, and then search for and select Azure AD B2C.
- Select User flows.
- Open the user flow that you previously created.
- Select Properties.
- Enable the Require ID Token in logout requests.
- Go back to Azure AD B2C.
- Select App registrations, and then select your application.
- Select Authentication.
- In the Logout URL text box, type your post logout redirect URI, and then select Save.
To require an ID Token in logout requests, add a UserJourneyBehaviors element inside of the RelyingParty element. Then set the EnforceIdTokenHintOnLogout of the SingleSignOn element to true. Your UserJourneyBehaviors element should look like this example:
Azure B2c Single Sign-on Configuration
To configure your application Logout URL:
- Sign in to the Azure portal.
- Make sure you're using the directory that contains your Azure AD B2C tenant by selecting the Directory + subscription filter in the top menu and choosing the directory that contains your Azure AD B2C tenant.
- Choose All services in the top-left corner of the Azure portal, and then search for and select Azure AD B2C.
- Select App registrations, and then select your application.
- Select Authentication.
- In the Logout URL text box, type your post logout redirect URI, and then select Save.
B2c Single Sign On Configuration Yahoo Mail
Next steps
B2c Single Sign-on Configuration
- Learn how to configure tokens in Azure AD B2C.